Manual VPN resolver check
DNS leak test
A DNS leak test shows whether your browser appears to resolve domains through the DNS path you expected. Use it after connecting a VPN, proxy, corporate network, or public Wi-Fi to catch ISP resolver exposure and country mismatches before sensitive browsing.
Example ping123 result screenshot
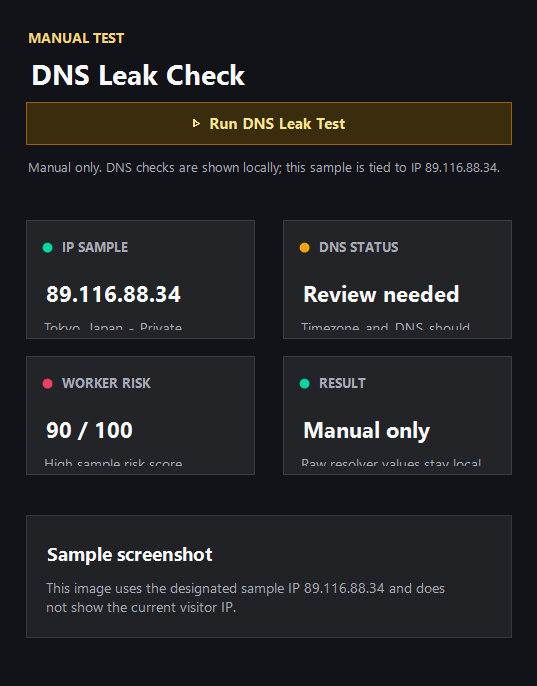
The screenshot below uses the designated sample IP 89.116.88.34, not a current visitor IP. Use it as a visual reference for the fields explained on this page.
What a DNS leak test checks
DNS turns domain names into IP addresses. If those lookups still go to your original ISP while the public IP uses a VPN exit, the session can reveal a network path you did not intend to expose.
The ping123 DNS workflow is manual: resolver-check requests are made only after you choose to run them, and the page explains whether the observed resolver path looks consistent.
How to read resolver results
A resolver from your VPN provider, chosen secure DNS provider, or expected corporate network can be normal. A resolver from your home ISP while the VPN is connected is a stronger leak signal.
Country mismatch matters when account region or privacy consistency matters. A public IP in one country and DNS in another country may trigger extra checks even if both services are legitimate.
Fix the exact DNS cause
DNS problems often come from browser secure DNS, router settings, operating system DNS, VPN split tunneling, or corporate policy. Change one setting at a time and rerun the test so you know what fixed the resolver path.
After DNS looks correct, run WebRTC and IP leak checks before logging into sensitive accounts.
What the result fields mean
Normal signals vs. risk signals
Usually normal
- Resolver provider matches the VPN, trusted secure DNS, or expected managed network.
- Resolver country is consistent with the public IP country and session purpose.
- The original ISP resolver does not appear while the VPN is active.
- Repeating the same test returns stable resolver results.
Needs attention
- DNS still points to the home ISP while the public IP uses a VPN.
- Resolver country conflicts with the account region or VPN country.
- Browser secure DNS bypasses VPN resolver settings unexpectedly.
- Router or corporate DNS policy forces a resolver you did not intend to use.
Next action
Check DNS after every network change
DNS leaks are easy to miss because the public IP can look correct while resolver traffic tells a different story.
Fixes and next steps
- Enable DNS leak protection in the VPN client.
- Disable browser secure DNS if it conflicts with your VPN resolver.
- Set OS DNS to the VPN provider or a trusted encrypted resolver.
- Check router DNS settings when every browser shows the same unexpected resolver.
- Restart the browser after DNS changes and rerun the same test.
- Pair DNS results with WebRTC and public IP checks before sensitive logins.
FAQ
What is a DNS leak?
A DNS leak happens when resolver requests use a network path outside the VPN or privacy route you expected.
Is public DNS a leak?
Not always. Public DNS can be intentional, but it should be expected and consistent with your session.
Why does secure DNS change my result?
Browser or OS secure DNS can override VPN DNS settings and send lookups to another provider.
Should I test DNS on public Wi-Fi?
Yes. Public Wi-Fi, captive portals, and managed routers can force DNS behavior that differs from your VPN settings.
What should I test after DNS?
Run a WebRTC leak test, public IP check, and browser privacy check to catch non-DNS mismatches.
Before you continue
Run the manual DNS probe before you trust the session
ping123 keeps DNS testing explicit so resolver checks happen only when you choose to run them.