Safe exposed-service scan
Online Port Scanner and Exposure Check
Check whether common ports are open before trusting a server, proxy, or account environment. The first version uses an allowlist of common ports and external probe nodes.
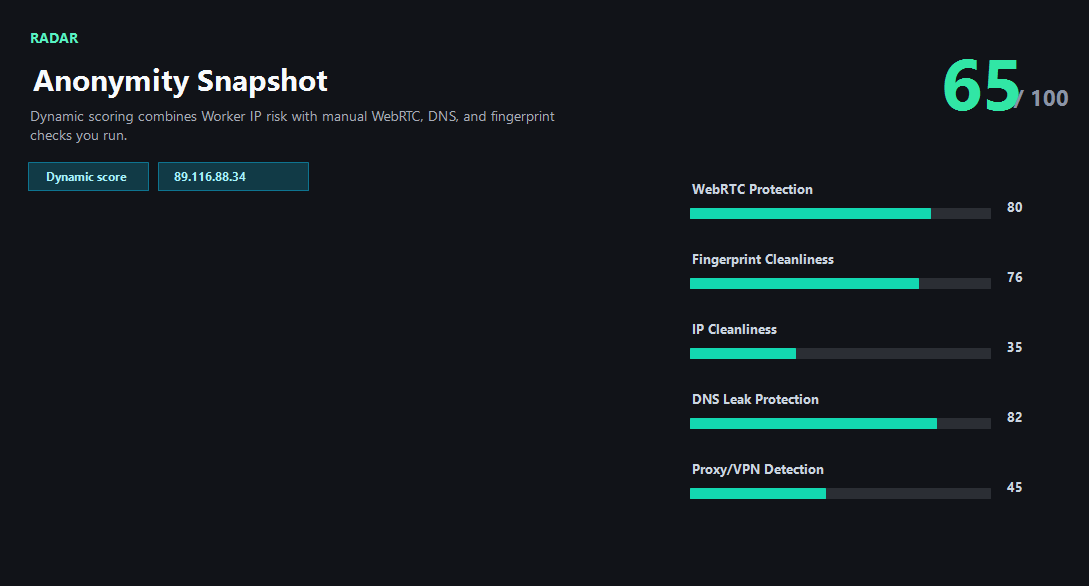
Example ping123 result screenshot
The screenshot below uses the designated sample IP 89.116.88.34, not a current visitor IP. Use it as a visual reference for the fields explained on this page.
What the scanner should and should not do
The scanner is intentionally limited to a common-port allowlist. It is meant for quick exposure checks, not broad vulnerability scanning.
External nodes perform the TCP checks. The Worker validates input, signs requests, and returns either scan results or a clear not-configured state.
What the result fields mean
Normal signals vs. risk signals
Usually normal
- Only expected web ports are open.
- Proxy and RDP ports are closed unless intentionally exposed.
- All locations agree on the same exposed services.
- Unexpected ports are fixed before account or production use.
Needs attention
- 1080 or 3128 is open on an IP meant to look like a normal user exit.
- 3389 RDP is exposed to the public internet.
- SSH is open on a server that should not be administered publicly.
- External scan nodes are not configured yet.
Next action
Treat exposed ports as part of IP quality
A clean reputation score can still be risky if the IP exposes proxy, RDP, or admin ports that do not match the expected environment.
Fixes and next steps
- Close public admin ports that are not required.
- Restrict SSH or RDP by firewall, VPN, or allowlist.
- Avoid using open-proxy exits for account-sensitive work.
- Retest after firewall or provider changes.
FAQ
Why only allowlisted ports?
The tool is for safe exposure checks, not broad scanning.
Can Worker scan ports directly?
The production design uses external probe nodes for TCP checks.
What does unavailable mean?
No external scan node is configured or the node could not return a result.
Before you continue
Combine exposure checks with reputation
Port exposure, IP type, abuse history, and platform-fit guidance should be read together before using an IP.