Fraud prevention signal check
IP fraud score checker
An IP fraud score estimates whether a network looks risky to anti-abuse, signup, payment, and account protection systems. The goal is not to label every VPN as bad, but to identify which signals can trigger review or friction.
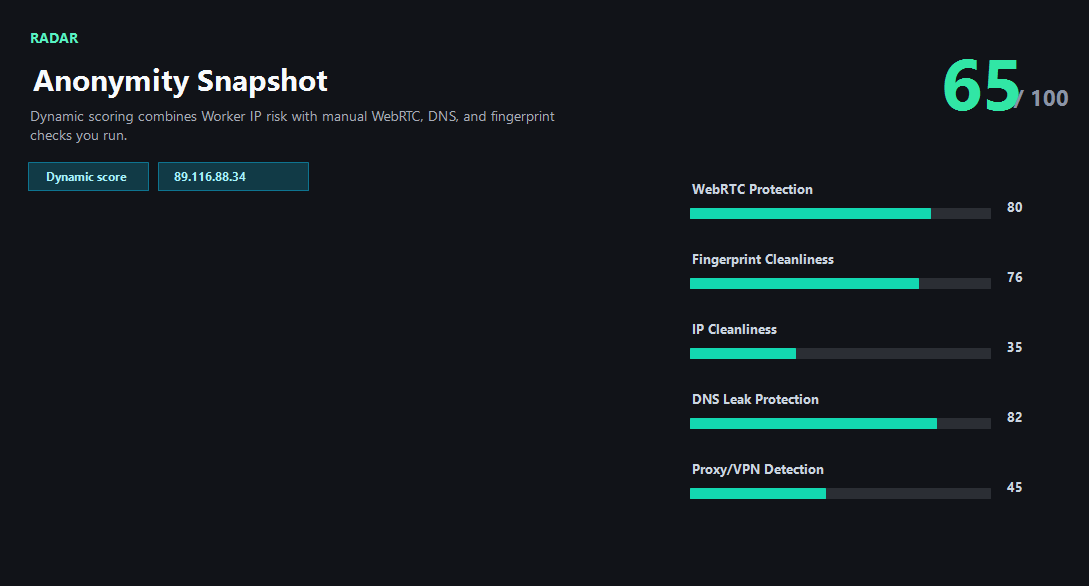
Example ping123 result screenshot
The screenshot below uses the designated sample IP 89.116.88.34, not a current visitor IP. Use it as a visual reference for the fields explained on this page.
What fraud systems often notice first
Fraud prevention systems commonly look at whether an IP belongs to a hosting provider, known VPN, proxy service, Tor exit, high-share residential pool, or network with recent abuse reports. They also compare geography, timezone, device, account age, and behavior.
A fraud score is therefore a triage signal. It tells you which network traits may create friction before you start a login, signup, checkout, or risk review test.
Proxy and VPN are not the only triggers
A clean VPN can be acceptable for privacy browsing, while a residential proxy with heavy abuse history can be risky. IPv6 leaks, DNS resolver mismatch, WebRTC exposure, or a browser timezone that conflicts with the IP can also push a session into review.
The fix depends on the cause. Rotating IPs helps abuse or blacklist problems; browser and DNS changes help leakage or consistency problems.
Use it for QA, not evasion
IP fraud score checks are useful for security QA, account risk troubleshooting, proxy quality testing, and understanding false positives. They should be used to reduce accidental mismatch, not to bypass legitimate controls.
When a score is high, document the trigger reason and test one change at a time so you can see whether the risk came from the network, browser, resolver, or account workflow.
What the result fields mean
Normal signals vs. risk signals
Usually normal
- Low fraud score and no obvious abuse reports.
- Network type matches the workflow and user expectation.
- IP country, timezone, DNS, WebRTC, and browser language are consistent.
- The IP is not a Tor exit or obvious high-share proxy node.
Needs attention
- High fraud score driven by Tor, proxy, datacenter, or abuse signals.
- A residential-looking IP has heavy shared-use or report history.
- DNS/WebRTC exposes a real ISP behind a VPN or proxy.
- The session changes IP country or ASN too frequently.
Next action
Find the trigger before changing the whole setup
A high fraud score can come from the IP, DNS, WebRTC, fingerprint, or region mismatch. Fixing the exact trigger is faster than random rotation.
Fixes and next steps
- Use a lower-risk network when the current IP is flagged as Tor, proxy, or high-abuse.
- Avoid datacenter exits for consumer account workflows that expect residential traffic.
- Fix DNS and WebRTC leaks before retesting the same IP.
- Keep timezone, browser language, and account region aligned with the IP country.
- Reduce rapid IP rotation during sensitive workflows.
- Document score changes after each adjustment so the cause is clear.
FAQ
What is an IP fraud score?
It is an estimate of how risky an IP may look to fraud prevention systems based on proxy, VPN, Tor, abuse, network type, and consistency signals.
Does using a VPN always create a high fraud score?
No. Some VPN exits are clean for privacy browsing, but shared datacenter exits can still trigger friction in account and payment flows.
Can residential proxies have fraud risk?
Yes. Residential IPs can become risky through shared abuse, blacklists, fast rotation, or leak mismatches.
What should I do with a high fraud score?
Identify the trigger first. Rotate only if the IP itself is the problem; otherwise fix DNS, WebRTC, browser, or region consistency.
Is this the same as bypassing fraud checks?
No. The purpose is transparency, QA, and troubleshooting false positives or accidental risk signals.
Before you continue
Run the visible checks before a sensitive workflow
ping123 makes the network and browser triggers visible so you know what to fix before a fraud review or login warning appears.