VPN, proxy, and anonymizer signals
VPN detection test
A VPN detection test checks whether the current IP looks like a VPN, proxy, Tor exit, hosting provider, residential network, or mobile carrier. Use it before account login, fraud QA, ad review, proxy buying, or any workflow where network trust matters.
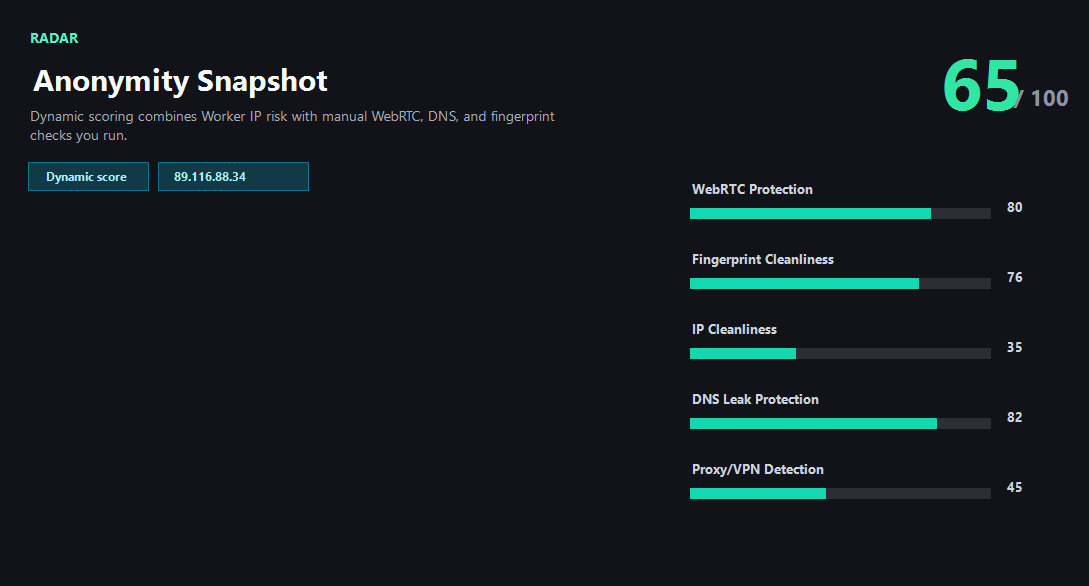
Example ping123 result screenshot
The screenshot below uses the designated sample IP 89.116.88.34, not a current visitor IP. Use it as a visual reference for the fields explained on this page.
VPN detection is not the same as a leak test
A VPN leak test asks whether your real network is exposed. A VPN detection test asks whether the visible IP itself is likely to be classified as VPN, proxy, Tor, hosting, residential, or mobile. Both matter, but they answer different questions.
For simple privacy browsing, a known VPN exit may be fine. For payments, ads, signups, marketplaces, developer dashboards, or fraud-prevention QA, that same VPN label can trigger additional checks.
What websites use to detect VPNs
Common clues include ASN ownership, hosting provider ranges, proxy/VPN databases, Tor exit lists, abuse reports, shared gateway behavior, DNS resolver mismatch, WebRTC candidates, timezone and language mismatch, and how frequently the session changes IP country.
No single clue is perfect. A datacenter IP can be legitimate, and a residential IP can still be abused. The useful result is a transparent list of reasons that explains why the session looks normal, uncertain, or risky.
How to use the result
If the IP is clearly hosting or VPN and your workflow expects a consumer network, switch to a better-suited exit before logging in. If the IP type is acceptable but DNS or WebRTC conflicts with it, fix the browser and resolver path before rotating the IP.
For teams, VPN detection works best as a preflight checklist: public IP, ASN, reputation, VPN/proxy/Tor label, DNS, WebRTC, timezone, language, and target account region.
What the result fields mean
Normal signals vs. risk signals
Usually normal
- ASN and organization match the network type you intended to use.
- No clear VPN, proxy, Tor, or abuse label appears.
- DNS and WebRTC do not expose another network path.
- Browser timezone and language fit the IP country and account context.
Needs attention
- Hosting or cloud ASN appears when the workflow expects residential traffic.
- VPN/proxy/Tor labels appear before payment, signup, or ad account activity.
- DNS or WebRTC exposes the original ISP behind the VPN or proxy.
- IP country, browser timezone, language, and account region conflict.
Next action
Decide whether detection risk matters for this task
A VPN label is not always bad. It becomes important when the site, account, payment, ad platform, or anti-abuse workflow is sensitive to anonymized traffic.
Fixes and next steps
- Use a residential or mobile network when the workflow expects consumer traffic.
- Avoid shared datacenter VPN exits for sensitive account or payment workflows.
- Fix DNS and WebRTC mismatches before blaming the IP itself.
- Keep timezone, language, and account region aligned with the chosen IP country.
- Retest after switching VPN nodes, proxy providers, browser profiles, or DNS settings.
- Log the IP, ASN, risk score, and trigger reason for repeatable QA.
FAQ
What is VPN detection?
It is the process of checking whether an IP address or session looks like VPN, proxy, Tor, hosting, or other anonymized traffic.
Can websites detect every VPN?
No. Detection varies by data source and behavior. Many systems use probability signals rather than a single perfect database.
Is being detected as VPN always bad?
No. It depends on the workflow. Privacy browsing may be fine, while payment, signup, ads, or account recovery can be more sensitive.
How is VPN detection different from IP reputation?
VPN detection focuses on traffic type and network classification. Reputation focuses more on abuse history, spam, blacklists, and trust.
What should I test after VPN detection?
Run DNS, WebRTC, IP risk, and browser fingerprint checks to confirm the whole session is consistent.
Before you continue
Check detection risk before the site checks it for you
ping123 helps you see the signals a trust or anti-abuse system may notice before you touch a sensitive workflow.